Setup
Use the/install-code-review command to set up automated code review for GitHub or GitLab:
- Detect your SCM platform (GitHub or GitLab)
- Verify prerequisites (CLI tools, permissions)
- Walk you through review configuration (depth, security, triggers)
- Create a PR/MR with the workflow files
How it works
Once enabled, the Droid Review workflow:- Triggers on pull request events (opened, synchronize, reopened, ready for review)
- Skips draft PRs to avoid noise during development
- Fetches the PR diff and existing comments
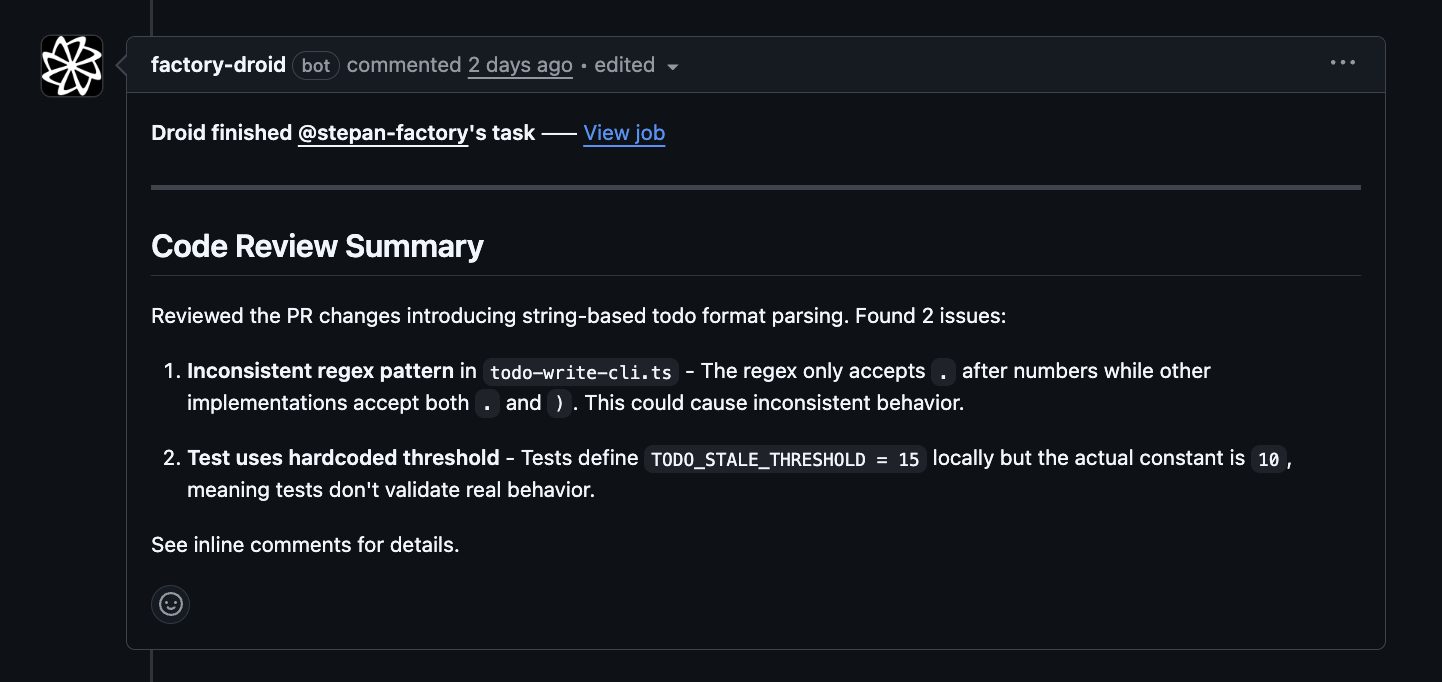
- Analyzes code changes for bugs, security issues, and correctness problems
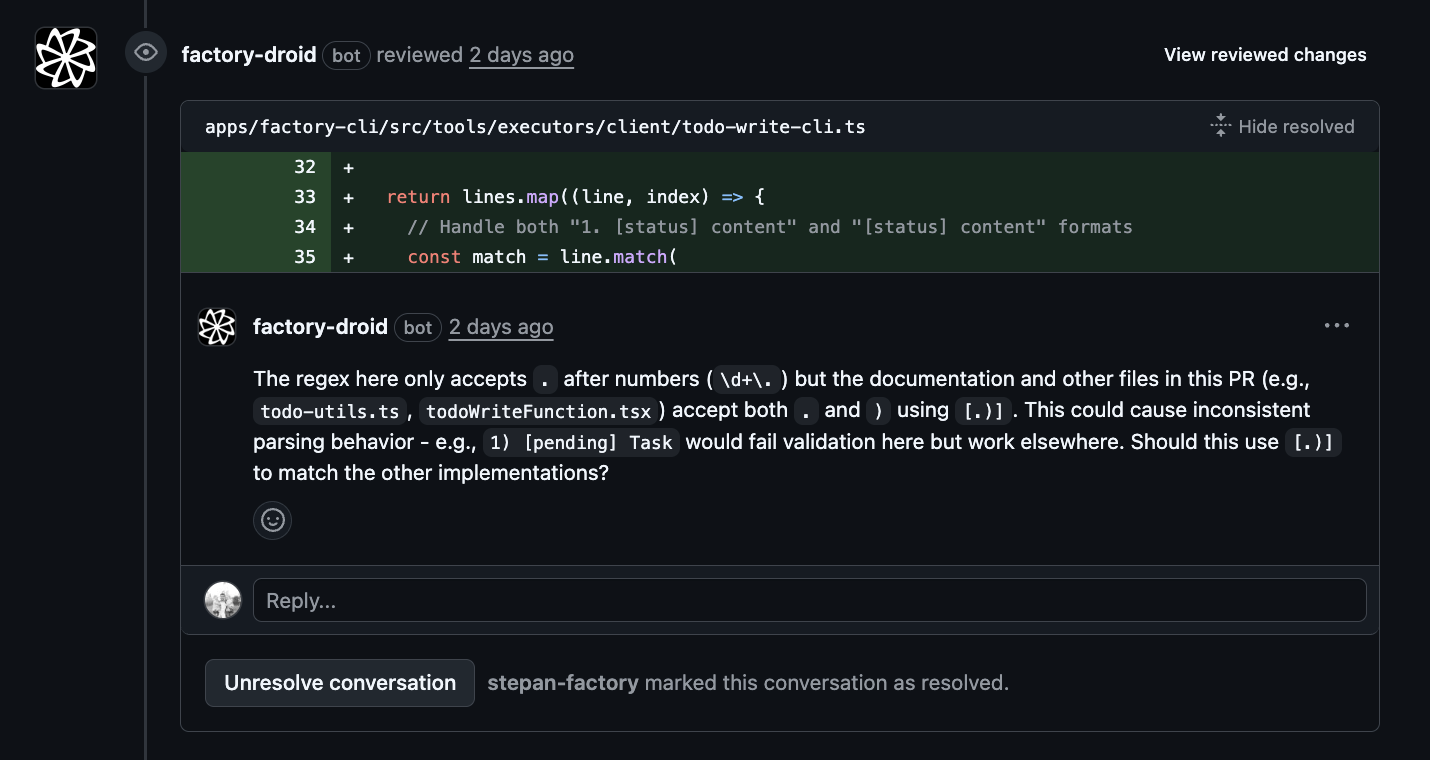
- Posts inline comments on problematic lines
- Submits an approval when no issues are found
Review depth
Thereview_depth input controls the thoroughness and cost of each review. You choose the depth during /install-code-review setup, or set it directly in your workflow.
deep(default) — Thorough analysis with higher reasoning effort. Catches more subtle bugs but costs more per review. Best for production code and security-sensitive repos.shallow— Faster, more cost-effective reviews that cover surface-level issues. Good for high-volume repos, draft PRs, or teams watching spend.
review_model and reasoning_effort, which take precedence over the depth preset.
Security review
Security review is a dedicated workflow for STRIDE, OWASP, OWASP LLM Top 10, and supply-chain analysis. See Security Review for automatic PR security reviews, scheduled scans, and local full-codebase audits with the built-insecurity-review skill.
What Droid reviews
The automated reviewer focuses on clear bugs and issues:- Dead/unreachable code
- Broken control flow (missing break, fallthrough bugs)
- Async/await mistakes
- Null/undefined dereferences
- Resource leaks
- SQL/XSS injection vulnerabilities
- Missing error handling
- Off-by-one errors
- Race conditions
Customizing the workflow
After the workflow is created, you can customize it by editing.github/workflows/droid-review.yml in your repository.
Change the trigger conditions
Modify when reviews run:Custom review guidelines
Add repository-specific review guidelines by creating a.factory/skills/review-guidelines/SKILL.md file in your repo:
Change the model
Use a different model for reviews:Skip certain PRs
Add conditions to skip reviews for specific cases:Limit comment count
Adjust the maximum number of comments in the prompt:All workflow inputs
| Input | Default | Description |
|---|---|---|
automatic_review | false | Automatically review PRs without @droid review |
review_depth | deep | Review preset: deep (thorough) or shallow (fast) |
review_model | (from depth) | Override model for code review |
reasoning_effort | (from depth) | Override reasoning effort |
include_suggestions | true | Include code suggestion blocks in comments |
See also
- Security Review - Security-focused PR reviews and full-codebase audits
- GitHub Integration Security - Security architecture for the GitHub App integration
- GitHub Actions examples - More automation workflows
- Droid Exec - Running Droid in CI/CD environments